Runtime Authorizations for Agents
AI without authorizations is a liability
Every integration added increases complexity. Every permission granted increases risk. Without governance, scaling AI becomes unmanageable.





Dynamic, auditable authorizations for the agentic era
Infrastructure Bottlenecks
One clear perimeter eliminates scattered resources and fragile integrations, unlocking company-wide reliability, operational speed, and scalable AI adoption.
Authorization Gaps
Contextual, task-based permissions replace static, overbroad access, ensuring agents act safely with only the precise rights required for each task.
Governance at Scale
Governance enables AI to operate at full power while mitigating risks, enforcing control, and preventing costly, irreversible business mistakes.

Boundaries for every agent
Use Denied to audit Agent tools usage, block commands, or redact unauthorized data.

Enforce authorizations at the agent level

the agent
Agent hooks or SDK

MCP Gateway or Middleware

the agent
Sandboxing
Runtime Security for your Agents
Implement granular authorizations that secure your Agents from executing unwanted actions and potential adversarial requests.

.webp)
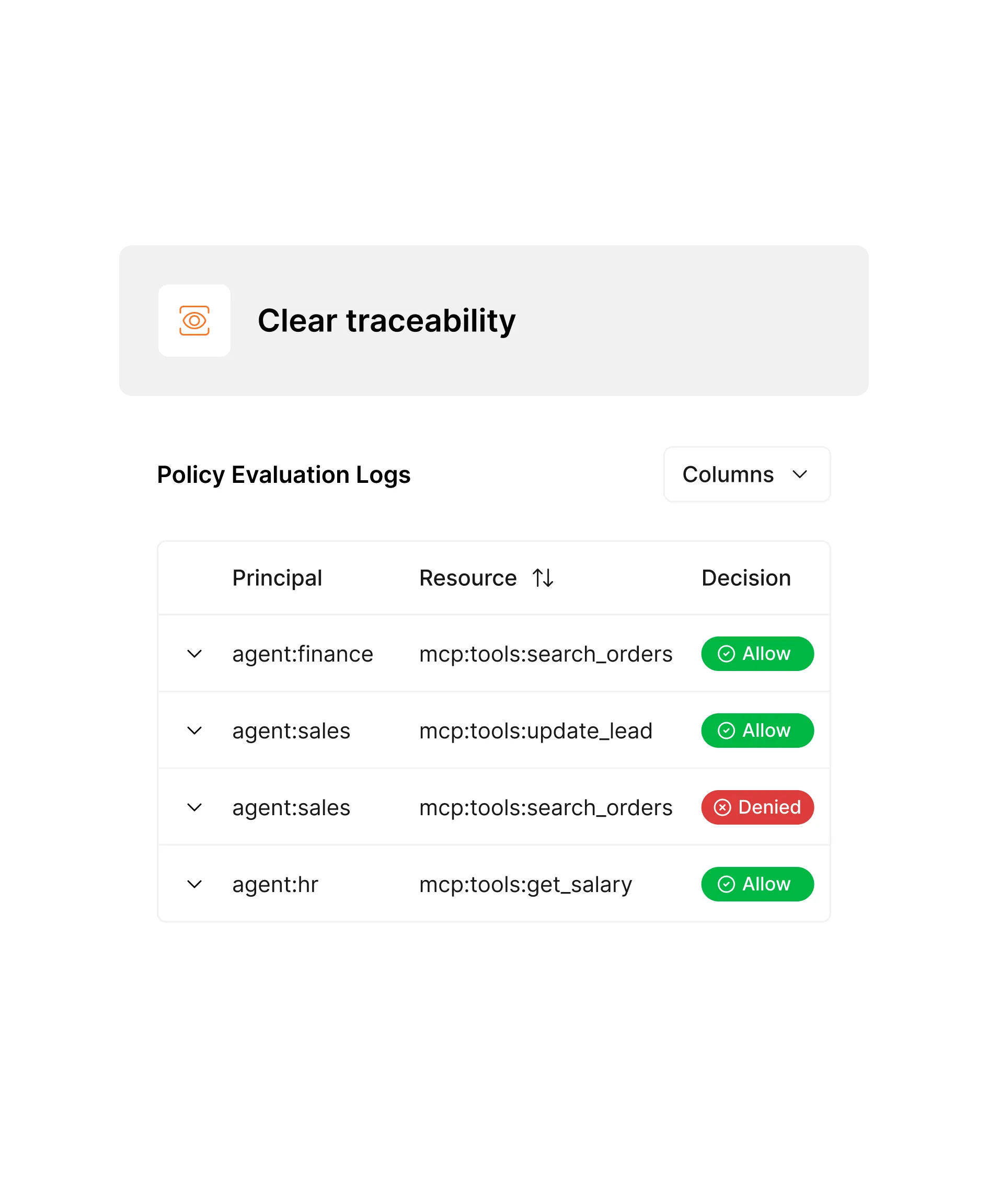
Enterprise-ready control at your fingertips
Monitor complex AI operations with intuitive tools that provide comprehensive visibility and control across your Agents.
- Policy-based Authorization
- Real-time performance monitoring
- Centralized policy enforcement

Real-time observability for Agent-driven actions
Monitor and audit each action taken by your Agents to guarantee accountability and transparency.

.svg)
.svg)
